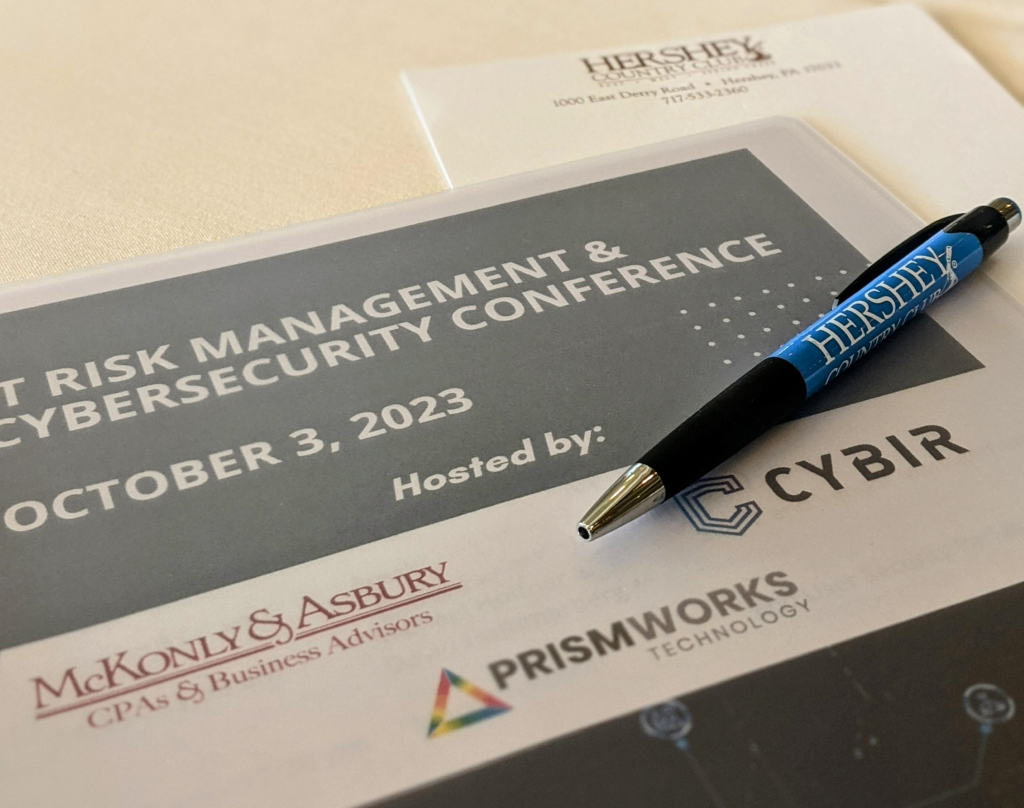
On October 3, 2023, over 60 IT professionals gathered for a day of learning and networking at the IT Risk Management & Cybersecurity Conference in Hershey, Pa. Prismworks Technology co-hosted the event alongside strategic partners McKonly & Asbury and CYBIR at the Hershey Country Club.
“Don’t wait to implement a vendor management process until you need one.”
David Hammarberg, Partner at McKonly & Asbury, and Chris Fieger, CPA and Supervisor at McKonly & Asbury, kicked off the conference with a presentation on SOC 2 and vendor management. The pair discussed the importance of taking time to identify critical vendors and the role SOC 2 plays in the process. They also stressed how timing was crucial in vendor management.
“I want to vet [vendors] before I need them, because when I need them, it might fall through the cracks,” Hammarberg said. “Don’t wait to implement a vendor management process until you need one.”
Hammarberg and Fieger’s session also touched on the differences between SOC 1 and SOC 2 reports, how to respond to a vendor who is hesitant to release reports, and why it is important for critical controls to be present in a SOC 2.
“Keep the odds in your favor.”
Keynote speaker Sunny Notani, Special Agent for the United States Secret Service, followed Hammarberg and Fieger’s presentation with a session on online scams. Notani discussed business email compromise (BEC), money mules, and a trending cryptocurrency investment scam called “pig butchering” where scammers trick their victims into giving them every dollar they have.
“Crypto is deregulated – it’s like the Wild West,” Notani said. “People have a hard time believing someone would go to these lengths [to scam], but they are professionals. It’s what they do. They’re very patient and they will wait it out.”
Notani reiterated the importance of training employees to be vigilant of scam attempts and to immediately file a report to local law enforcement if someone falls victim to a scam. He recommended everyone should take personal security measures against scams and attacks to keep the odds in their favor, but to remember threat actors will always look for ways to get past them.
“The internet is a bad neighborhood, and we all live there.”

Mark Crescenzi, President at Prismworks Technology, anchored the morning presentations with a lesson on end user security. When analyzing risk, Crescenzi said organizations should consider the likelihood of an occurrence and how bad the situation could get as a result. He also recommended the use of a risk matrix to help determine what areas to focus on and how to prioritize when mitigating risks.
Crescenzi walked attendees through the multiple layers of end user security, starting with the “low hanging fruit” security measures that every organization should be implementing. These low effort but highly effective measures include MFA for email and VPN, backup, and automated server/workstation patching.
“The internet is a bad neighborhood, and we all live there, so lock your doors. Anyone can come up and try to get in – and there’s no consequence,” Crescenzi said.
“It does not take a huge amount of talent, knowledge, or effort to do a cyber-attack.”
Ken Pyle, Partner at CYBIR, led the afternoon sessions with a presentation about current security vulnerabilities. Pyle noted how society is experiencing an exploitable cultural shift and generational rollover, creating an environment that makes individuals very susceptible to cyber attacks. And with the emergence of technology like artificial intelligence (AI) and large language models (LLM), it is getting easier for threat actors to disrupt systems and for victims to let their guard down.
“It does not take a huge amount of talent, knowledge, or effort to do a cyber-attack,” Pyle said. “Will you ever stop finding vulnerabilities? The short answer is no. There’s no such thing as 100%. Nobody is looking out for you but yourself.”
“These systems are acting more human than most of the things we’ve done in the past.”
Jamison Rotz, Founder and CEO of Nearly Human AI, tagged in as the final speaker of the day with a session on data security in the age of AI. According to Rotz, whether it is used for good or bad, AI is here to stay. As new applications and more integrations are released, it is important to consider the risks associated with the technology and how to strategically manage them.
“The trouble with generative AI is it’s very disorienting. It’s going to be very difficult to know if you’re dealing with a real person or a bot. These systems are acting more human than most of the things we’ve done in the past,” Rotz said.
To responsibly navigate the risks posed by AI, Rotz recommended staying current on AI updates using reliable and timely resources. He also advised business leaders to create a policy outlining how they want their company to behave regarding the technology, and offer secure, alternative tools to employees to use in lieu of risky AI models.

